Cyber Security Threat-Update
Overview
- Current Events – White House, FBI and CIA have confirmed escalating cyber-attacks from Russia and non-state sponsored hackers, in the past 3 days.
- Risk – traditional Windows Servers used for File storage and Email are highly vulnerable to malware and ransomware attacks because they allow these 3rd party agents to be installed and run on the server without detection. Usually through basic business practices like opening emails or documents.
- Solution – Move files to secure cloud storage like your M365 Tenant, SharePoint
- How? – the HingePoint Road Map you are considering starting includes a Security First approach, where we migrate and secure your documents in Microsoft Tenant, where it is safe.
- Ready? – would like to expedite your implementation? We will adjust the plan to accelerate the migration to the cloud.
Background
We are providing a resource guide for our clients to help make them aware of the real threats to cyber security in 2022. The desire is to help them assess and secure their sensitive and critical company information in an ever-evolving business world. We understand you are in the process of modernizing and migrating your company files and documents into the cloud and a secure environment. There are significant signs that cyber-attacks are only going to increase, and companies must look for ways to reduce their risk. We are here to inform our clients how to protect themselves from these threats.
Having a network architecture of local file servers in 2022 is becoming a major liability, rather than a valued business asset. Now that our own government has told US businesses twice in the past two weeks to get ready for attacks, we need to take heed. Fortunately, when you implement this modernization strategy, you will be freeing yourselves from an attack that, at the very least, could just cause a major “fire drill”. At the worst ransom attacks lock all your files and you can’t get them back without paying the ransom (this usually take months even if you cooperate with the hackers). But if you can get to the safety of the M365 cloud (or alternative secure location), like so many of our other clients, then you will be able to experience a comfort level to know your business is better positioned for success in the 21st century. These core security values will be the cornerstone of how we provision your Microsoft 365 environment. Everything on your road map will be executed with an eye on security. And the security and risk strategy that we will help you employ will significantly reduce your risk to ransomware.
Microsoft published an article last month called “Overview of the security pillar,” and in it Microsoft said ‘Attackers now freely exploit vulnerabilities in system configurations, operational practices, and the social habits of the systems’ users. As system complexity, connectedness, and the variety of users increase, attackers have more opportunities to identify unprotected edge cases. Attackers can hack systems into doing things they were not designed to do.’ It is a great article that details many of the same key core components to our road map. We employ these strategies and leverage Microsoft’s massive security resources to secure our clients’ data. The primary strategy that Microsoft says that businesses should adopt is to Assume a Breach or Zero Trust approach. Read from Microsoft:
https://docs.microsoft.com/en-us/azure/cloud-adoption-framework/secure/
https://docs.microsoft.com/en-us/azure/architecture/framework/security/overview
Percentage of Ransomware Attacks by Industry
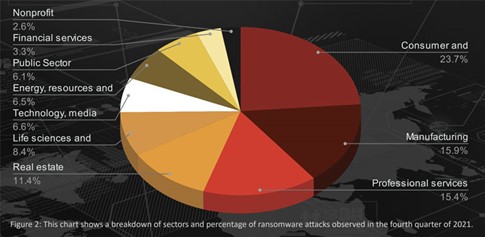
In the graph above, the threat to the Energy and Resources sector is at 6.5% but the Real Estate sector is almost double that risk at 11.4%. (4th highest risk on the graph)
Other Cyber News
Russia Prepping for Cyber Attacks
President Joe Biden says Russia is exploring options for cyberattacks. In a Wall Street Journal article yesterday, the president reiterated previous warnings for businesses to improve their cybersecurity. Citing recent intelligence that Russia is looking for options on how to attack the US.
“You have the power, the capacity, and the responsibility to strengthen the cybersecurity and resilience of the critical services and technologies on which Americans rely,” Mr. Biden said.
https://www.wsj.com/livecoverage/russia-ukraine-latest-news-2022-03-21/card/biden-says-russian-government-is-exploring-options-for-cyberattacks-lKF4al4DrVApvVYsW4IA?mod=e2li
FBI Warns of Energy Sector Attacks
‘It comes as the FBI has seen five U.S. energy companies have their systems scanned, according to a source familiar with the situation, outlined in an agency bulletin first reported by CBS News. ABC News has confirmed the bulletin’s contents.’
https://www.cbsnews.com/news/russia-cyberattacks-us-energy-fbi-warning/
Hacker Group Claims Access to user Authentication Firm Okta
Gizmodo published an article saying that hacker group LAPUS$ posted screenshots claiming it had achieved administrator access to Okta, a user authentication, and data management company. The group claims it is only focusing on Okta customers and suggested that they have had access to Okta’s system for months.
https://gizmodo.com/hacker-group-claims-extraordinary-access-to-user-authen-1848684491




